
As most people involved in WeAreNotWaiting are aware, on June 27th, the FDA issued a warning about cybersecurity issues with older medtronic pumps.
These happen to be the pumps that many people use on a day to day basis with systems such as OpenAPS and Loop.
Initially, it looked as though the FDA was attempting to revisit an old event, then on a second look, it seemed as though it was driven by Medtronic, however, further information revealed by Wired paints a very different picture.
But first, let’s step back in time to 2011.
2011 – Hacking insulin pumps for fun
There were numerous reports back in 2011 about a hacker managing to wirelessly control their insulin pump (something that is now at the core of OpenAPS and where Loop started from), that hacker being Jerome Radcliffe.
It made fairly sensational headlines at the time, although when you look at the small print, it’s perhaps less of an issue than it may have seemed. McAfee joined in shortly afterwards and managed to make it a more robust hack, requiring less information to take over the pump (essentially, none).

Following this event, nearly 10 years ago, Medtronic made changes to their pump systems to eliminate this “vulnerability”, however, there was no recall, suggesting that it wasn’t considered that serious a risk back in 2011.
2019 – The Medtronic recall
Stepping forward eight years, everything has changed.
Medtronic have recently announced an ACE (Alternate Controller Enabled) pump that will work with Tidepool Loop; the FDA approach to hybrid closed loops has taken a componentised approach allowing manufacturers to make a single component that should be interoperable with other components; and Medtronic have released the first “Artificial Pancreas” in the 670G (to mixed reviews), with another in the pipeline (780G) for public release in around 12 months time.
And then all of a sudden, the FDA issued a press release that starts with the statement:
The U.S. Food and Drug Administration is warning patients and health care providers that certain Medtronic MiniMed insulin pumps are being recalled due to potential cybersecurity risks and recommends that patients using these models switch their insulin pump to models that are better equipped to protect against these potential risks. To date, the FDA is not aware of any confirmed reports of patient harm related to these potential cybersecurity risks.
At the same time, this letter was sent to known users of “older” Medtronic pumps letting them know of a Cybersecurity risk associated with the pumps. Quoting the letter verbatim:
URGENT FIELD SAFETY NOTIFICATION
MiniMed™ 508 Insulin Pump and MiniMed™ Paradigm™ Series Insulin Pumps Cybersecurity ConcernsJune 27, 2019
Dear Valued Customer:
You are receiving this letter because our records indicate you may be using a MiniMed™ 508 insulin pump or a MiniMed™ Paradigm™ series insulin pump. Because your safety is our top priority, we are making you aware of a potential cybersecurity risk.
Potential cybersecurity risk:
The MiniMed™ 508 insulin pump and the MiniMed™ Paradigm™ series insulin pumps are designed to communicate using a wireless radio frequency (RF) with other devices such as a blood glucose meters, glucose sensor transmitters, and CareLink™ USB devices.Security researchers have identified potential cybersecurity vulnerabilities related to these insulin pumps. An unauthorized person with special technical skills and equipment could potentially connect wirelessly to a nearby insulin pump to change settings and control insulin delivery. This could lead to hypoglycemia (if additional insulin is delivered) or hyperglycemia and diabetic ketoacidosis (if not enough insulin is delivered).
IMPORTANT NOTE: At this time, we have received no confirmed reports of unauthorized persons changing settings or controlling insulin delivery.
It then goes on to suggest that you speak with your healthcare professional about changing your pump, and outlines a number of ways in which you can limit the risk with the pumps, including not giving out your pump serial number and not connecting to any third-party devices or use any software not authorized by Medtronic. There has also been talk of users being told that their healthcare teams have stated they won’t support use of these pumps (although this is hearsay at the moment).
It looks as though an FDA announcement has driven the Medtronic activity, but then, on July 1st, there is a second FDA Safety Communication that seems to have originally been issued on the 27th June which states:
The FDA is warning patients and health care providers that certain Medtronic MiniMed™ insulin pumps have potential cybersecurity risks. Patients with diabetes using these models should switch their insulin pump to models that are better equipped to protect against these potential risks.
Medtronic is recalling the following affected MiniMed pumps and providing alternative insulin pumps to patients.
What’s notable about the new statement is that it states that Medtronic is recalling the pumps. You’ll note the new language that’s been included. It all seems a little strange.
Then, on the evening of Tuesday 16th July, Wired magazine released this article, and all of a sudden it all became clear. To quote:
TWO YEARS AGO, researchers Billy Rios and Jonathan Butts discovered disturbing vulnerabilities in Medtronic’s popular MiniMed and MiniMed Paradigm insulin pump lines. An attacker could remotely target these pumps to withhold insulin from patients, or to trigger a potentially lethal overdose. And yet months of negotiations with Medtronic and regulators to implement a fix proved fruitless. So the researchers resorted to drastic measures. They built an Android app that could use the flaws to kill people.
Now it’s worth having a read of this article. Two years ago, OpenAPS and Loop were well established and had many users, and this feature of the old Medtronic pumps was very well known in diabetes technology circles. Six years previous to their “discovery”, as already mentioned, Jerome Radcliffe (And McAfee) had identified this very same issue (as had others, including Ben West, who’d tried to use it for good rather than highlight it as an issue).
So it wasn’t exactly new. But what had they done that’s different this time?
The details?
Again, quoting from the Wired article:
MiniMed pumps also come with remote controls, which basically look like car key fobs, and offer a way for caregivers or medical professionals to control the pumps instead from a short distance.
But as Rios and Butts discovered, it’s relatively easy to determine the radio frequencies on which the remote and pump talk to each other. Worse still, those communications aren’t encrypted. The researchers, who also include Jesse Young and Carl Schuett, say they found it easy to reverse engineer the simple encoding and validity checks meant to protect the signal, enabling an attacker to capture the fob’s commands. A hacker could then use readily available, open source software to program a radio that masquerades as a legitimate MiniMed remote, and send commands that the pumps will trust and execute. After establishing that initial contact, hackers can then control that radio through a simple smartphone app to launch attacks—similar to apps that can fill in for your television remote.
So essentially they’d worked out that they could hack into the remote and use that to issue commands. Now at this point, it looks like they’d not bothered doing any research, as it would have been much easier to go out and buy a RileyLink or Edison and Explorer board to do this, after all, they tend to have a better range than the remote and were freely available at the time.
Next they decided to go a step further, and created an app to do the grunt work, which included a brute-force attack that cycles through the permutations of six figure serial codes that are available, so that eventually, you’ll get the correct one. The reality is that’s a fairly quick process, as in the grand scheme of things, there aren’t that many! The article discusses that they were still using the “malicious remote” to do this, suggesting they weren’t aware of the various radio transmitters used by OpenAPS users with a far greater range.
They then took this to the FDA and showed them how, in a room full of people using these older pumps, they could press a button, override all settings and then deliver a massive bolus dose of insulin or suspend the pump, or, as QED Secure Solutions’ Carl Schuett said:
An attacker could then simply press buttons in the app to repeatedly give a patient doses of insulin, or override a patient’s attempts to give themselves insulin.
Now wait a second. This is an old Minimed x22, x23 or x54 pump. It delivers insulin at a rate of 1.5u per minute. To give a massive dose of insulin takes a long time. 25u (the max bolus allowed) would take over a quarter of an hour. If you’re going to use this technique to try and kill someone with multiple doses, using the “Malicious remote” you’re likely to be in their face for a very long time. Someone has to notice that. The article mentions a more powerful antenna would make this more effective, but suggests this wasn’t tried.
Secondly, if you suspend the pump, or reset basals to zero, again, a patient is likely to notice that as well. Suspending it results in it beeping or buzzing at you every 5 minutes. Setting a very low dose would result in a slowly increasing glucose level and is likely to result in someone taking action.
So while, technically, yes, there’s a risk, the reality of this situation is that it hasn’t really changed all that much from 2011. Yes, someone’s implemented what McAfee talked about in 2012, but it’s not very different.
The reality is that, faced with this sort of demonstration, the FDA and Medtronic would have had little choice but to make the announcement that they did.
So what’s the impact?
In the article, Medtronic disputes it being a recall, and the FDA acknowledges loopers, with their representative saying that a full recall would have been impractical and counterproductive, due to their use by this group.
And that’s where it becomes interesting.
A significant number of users of these types of pumps are now using them in some form of DIY system. Given the way that OpenAPS manages radio signals, and when you consider how it works when you’ve got it running alongside Loop, where it effectively stops the RileyLink from connecting, the ability of the app (in it’s proof of concept form at least) to get a decent connection to a pump of an OpenAPS user would be a challenge.
Secondly, the loop would, on receiving the changed data from the pump, immediately set a zero TBR, and in the case of OpenAPS, dependent on setup, warn you that you need a bunch of carbohydrate to avoid a low.
And finally, if you aren’t using one of these pumps for DIY use, would you still be vulnerable?
When they shipped, I believe that the “Remote” option was disabled, and dependent on the jurisdiction (certainly from what I’ve seen in Europe – I can’t speak for the rest of the world) the remote was not part of the package for most people. This would mean that, even if someone had access to a super-boosted antenna, an out of the box pump wouldn’t be affected by it as the communications channel simply wouldn’t be switched on.
The alert appears to be more of a warning than anything else. But perhaps there are other things going on in 2019 that also affect what has happened.
2019 shenanigans and the part they play
Right now, if there were no DIY systems, then there’d be no noise about how the DIY systems outperform the 670G. There wouldn’t be the few thousand people worldwide using these systems and there wouldn’t be a healthy black market for the older medtronic pumps. In the US especially, where most of the Bluetooth enabled pumps that are around in the rest of the world are not available, so these are not an option for those wanting to use some sort of DIY loop. By removing these pumps from production, you’d be rapidly shutting down the use of DIY solutions by many people, or at least generating a level of concern amongst prospective loopers.
Alongside that, the introduction of an ACE pump with Tidepool, which has a clearly defined, if not necessarily accessible protocol means that Medtronic is moving out of being the 700lb gorilla in the corner with the artificial pancreas technology, to being the 1,000lb gorilla able to supply pump tech for whatever artificial pancreas you might want alongside its own technology.
As an aside, wouldn’t it be great if this was interoperable with existing DIY technologies with a published protocol?
Or is it simply a ploy to try and encourage those likely to be joining the DIY movement for the first time now, who were not in the vanguard, to wait for the 780G?
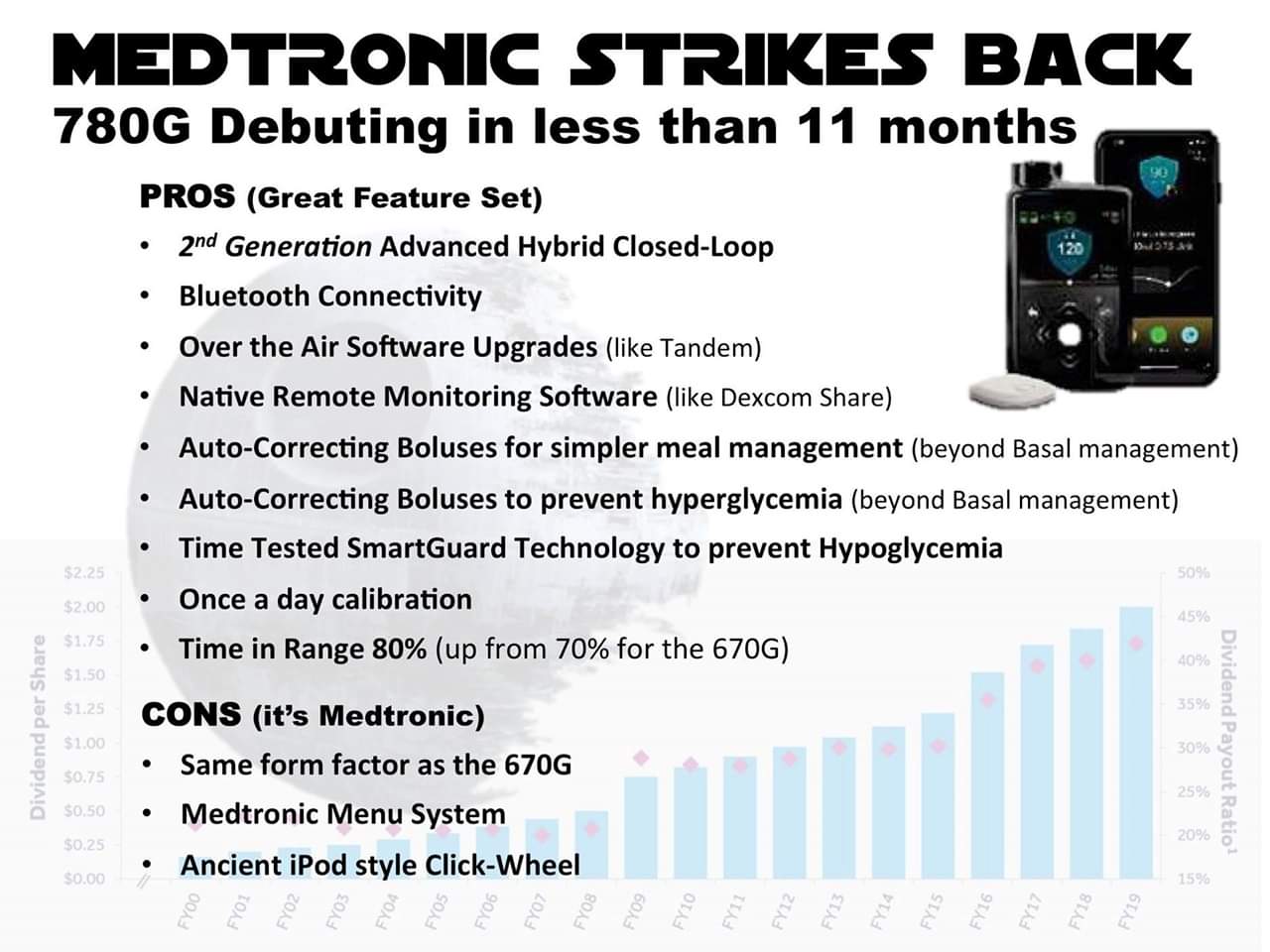
After all, the feature list of the 780G, shown below is pretty impressive, with a target of 100 mg/dl and potentially offering functionality that could be as good as that you get in some of the DIY systems (packaged, of course, in a Medtronic black box with the sadly familiar interface), and doesn’t have this security feature.
Regardless, it feels like this is a case of shutting the stable door after the horse has bolted. The number of pumps in the recall is relatively low, a specific configuration on the pump is required, and there are other points of significance that cause the risk of interference to remain remarkably low.
And if you’re using one in a DIY system, you’ll be less likely to have put yourself in hospital as a result of an insulin muck up than someone using a standard pump, or to have been subject to the “recall” of a pump with stuck buttons, which affects 117,239 pumps. Thirty times more than the vulnerability which we are discussing here.
To close, I’ll leave you with the thought from both Medtronic and the FDA that I think sums it up for me:
At this time, we have received no confirmed reports of unauthorized persons changing settings or controlling insulin delivery.
Excellent article! I hope many will take the time to read it through. I Loop. Loop is a game changer in my opinion. It appears to me that Medtronic’s strategies and vertical business model have suppressed technology improvements, and now that its profits are being pressured by companies such as Tandem, they are striking out . In the process, they are alienating many people, including me, who are long term users of their products. I have asked Medtronic to respond to the question, “if security is such an important issue now, why wasn’t it important to you when the issue was originally discovered?” So far, they have not given a response that addresses the question. I had a Paradigm with remote at the time, and, as a tech worker, I was very disappointed that Medtronic took no action to fix or replace the affected pumps – too much impact th their bottom line, I assume. I’m thankful there are real alternatives to Medtronic now, and I will be moving from a Loop to Tandem when I am eligible next year.